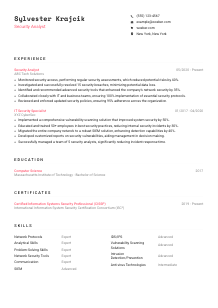
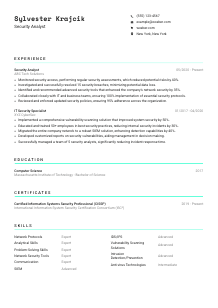
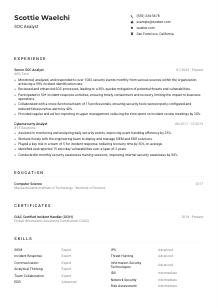
Security Analyst CV Example
Shielding networks, but your CV lacks defense mechanisms? Navigate threat to opportunity with this Security Analyst CV example, molded using Wozber free CV builder. Grasp how to encrypt your cybersecurity skills to match job requirements, ensuring your career is always locked out for your rivals.

How to write a Security Analyst CV?
Ahoy there, future Security Analyst trailblazer! The digital world's safety rests on shoulders like yours, and what better way to step into this role than with a CV that not only meets but exceeds every expectation? This isn't just about documenting your journey; it's about storytelling in a way that aligns perfectly with your dream role. With the help of Wozber's free CV builder, we're diving deep into the art of crafting a CV that is not only ATS-compliant but also resonates with your essence as a Security Analyst.
Ready to unlock the secrets? Let's decode this cipher together!
Personal Details
The gateway to your CV, the Personal Details section, is your digital handshake. It's where first impressions are formed, and trust me, we want this impression to be as impactful as a secure, encrypted connection. Let's ensure your introduction is not only accurate but also a beacon signaling your readiness for the Security Analyst position.
1. Name as Your Brand
Think of your name as the secure key to your professional profile. Display it prominently, akin to how a firewall stands guard, ensuring it's the first thing to catch the recruiter's eye with a clean, professional font.
2. Aligning with Your Role
"Security Analyst"—seeing this title right off the bat assures the hiring manager that they've found what they're searching for. This alignment acts like matching a key to a lock, opening the door to further consideration.
3. Essential Contact Details
Just like securing a network, your contact information should be fail-proof. Double-check your phone number and email address for accuracy—think of it as verifying digital certificates before establishing a connection.
4. Location, Location, Location
Specifying "New York, New York," directly responds to the job's location requirement. It's like setting up a geo-fence, immediately signaling to employers that you're within the operational perimeter.
5. Professional Links
Including a link to your LinkedIn profile is like adding a multi-factor authentication layer to your CV. It adds depth, providing recruiters with additional layers of your professional persona to explore.
Takeaway
Your Personal Details section isn't just information; it's the first line of defense, setting a professional and prepared tone. Think of it as your digital business card. Keep it neat and perfectly aligned with the job post. This is where the journey into your cybersecurity expertise begins!





Experience
In the realm of cybersecurity, your experience is your armor. It's the tangible proof of battles won and lessons learned. Crafting an Experience section that reflects your readiness and suitability for the Security Analyst role requires more than just listing your past jobs; it requires strategy and precision.
- Monitored security access, performing regular security assessments, which reduced potential risks by 40%.
- Investigated and successfully resolved 15 security breaches, minimizing potential data loss.
- Identified and recommended advanced security tools that enhanced the company's network security by 35%.
- Collaborated closely with IT and business teams, ensuring 100% implementation of essential security protocols.
- Reviewed and enforced updated security policies, ensuring 95% adherence across the organisation.
- Implemented a comprehensive vulnerability scanning solution that improved system security by 50%.
- Educated and trained 50+ employees in best security practices, reducing internal security incidents by 30%.
- Migrated the entire company network to a robust SIEM solution, enhancing detection capabilities by 40%.
- Developed customized reports on security vulnerabilities, aiding management in decision making.
- Successfully managed a team of 5 security analysts, significantly reducing incident response time.
1. Decipher the Job Description
Start by treating the job description like a security briefing. Extract the crucial requirements - perhaps it's experience with "security access monitoring" or "security breach investigations." These are the keywords you'll need to include in your narrative.
2. Structure with Precision
Organize your experiences like you're architecting a secure network. Begin with your current or most recent role and architect backwards. This order helps demonstrate your growth trajectory and up-to-date expertise in the field.
3. Targeted Accomplishments
For each role, craft bullet points that mirror the job's demands, similar to configuring security rules specific to an environment's needs. Did you "Monitor security access"? How many "security breaches" did you investigate? Quantify your impact wherever possible - numbers are persuasive and provide scale.
4. Quantifying Success
Including metrics provides a benchmark for your success, much like how security threat levels are assessed. Have you reduced incidents by a certain percentage or improved system security measurably? These numbers speak volumes.
5. Relevancy is Key
Stick to the script—include only what's directly pertinent to your role as a Security Analyst. Unrelated accomplishments, while impressive, are like open ports in a firewall; they divert attention from what's truly important.
Takeaway
Imagine your Experience section as your professional defense system. It's designed to protect but also to impress. Let each bullet point serve as evidence of your expertise and readiness to take on the Security Analyst role. Make it impossible for the hiring manager to pass you by!
Education
In cybersecurity, as in many tech fields, your educational background lays the foundation. It's the bedrock upon which your skills and experiences are built. Crafting this section to reflect the Security Analyst requisites is about showing you have the theoretical grounding to back up your practical expertise.
1. Identify Key Requirements
The job post asks for a "Bachelor's degree in Computer Science, Information Technology, or a related field." This is your guideline. Your degree title should directly correlate, ensuring there's no doubt you meet this foundational criterion.
2. Present with Clarity
Lay out your academic qualifications clearly. Start with your degree, followed by the institution, and then the graduation date. Think of it as building a secure, easily navigable database of your educational achievements.
3. Degree Specifics
For the Security Analyst role, your degree in "Computer Science" is a direct match. Highlight any specialization if applicable, akin to showcasing your niche in a broad spectrum of cybersecurity disciplines.
4. Pertinent Courses
If specific courses you've taken directly relate to the skills required in the job description - such as network security or cryptography - list them. This shows a direct link between your education and the job's requirements.
5. Additional Accolades
Mention any honors, clubs, or relevant projects if they add value to your candidacy for a Security Analyst position. However, balance is key; keep the focus on what truly strengthens your application.
Takeaway
Your education section is a testament to your preparedness for the cybersecurity battlefield. It underlines your theoretical expertise, providing a strong foundation for the practical skills you've acquired. Craft this section to highlight the key aspects that align with a Security Analyst's role and you'll be setting yourself up for success.
Certificates
In the cybersecurity realm, certifications are like badges of honor. They not only validate your skills but also show a commitment to staying abreast of the latest threats and defenses. Let's navigate how to showcase your certifications in a way that aligns with the Security Analyst position.
1. Match Key Job Requirements
Refer back to the job post which suggests, "Certifications such as CISSP, CISM, and Security+ are a plus." If you have these, they deserve a spot front and center. They're like the verified badges on your professional profile, signifying your expertise.
2. Select Relevant Certifications
Focus on listing certifications that are most relevant to the job description. It's about quality, not quantity. Similar to choosing the right security framework for a system, pick the certs that best match the job's defenses.
3. Dates Matter
For each certification, include the date acquired or the validity period. This shows recency and relevance, much like ensuring your software's security patches are up to date.
4. Continuous Learning
Cybersecurity is an ever-evolving field. Regularly updating your certifications and pursuing new ones demonstrates your dedication to keeping your skills sharp—akin to running routine security audits on a network.
Takeaway
Let your certifications section be a showcase of your continuous commitment to excellence and learning in the field of cybersecurity. Present it as evidence of your proactive stance on personal and professional development, ensuring you're always ready to face the latest cyber threats head-on.
Skills
A well-crafted Skills section is like having the best security protocols in place—it shows you're prepared for anything. In the case of the Security Analyst role, it's crucial to align this section with the job description to prove you have the necessary toolkit.
1. Decoding the Job Post
Begin by extracting both the explicit and implicit skills mentioned in the job description. Skills like "proficiency with security tools" and "strong analytical skills" are your keywords here. These are the tools in your security belt.
2. Prioritize Matching Skills
List your skills with a focus on those that directly align with the job requirements. Think of it as configuring your CV's firewall to allow only relevant traffic—your most applicable skills—to come through.
3. Order and Neatness
Structure your skills section neatly, prioritizing them from most to least relevant. This hierarchy makes it easier for hiring managers to scan through and match your skills with their needs, much like sorting data packets for efficiency.
Takeaway
Your Skills section is a concise inventory of the tools you wield in the cybersecurity landscape. Tailor it to the job description, and you'll show prospective employers that your skillset is not just extensive but also a perfect match for their needs. Let your expertise shine brightly here!
Languages
In the global field of cybersecurity, the ability to communicate across cultures can be just as critical as technical prowess. Whether it's documenting incidents or liaising with international teams, linguistic skills can play a pivotal role. Let's tailor the Languages section to spotlight your communicative assets.
1. Analyze Job Language Requirements
First, verify if the job posting specifies language needs. In our case, "strong English language competence" is a requirement, positioning your proficiency in English as a primary entry in this section.
2. Prioritize Key Languages
List languages in order of relevance to the job, starting with those explicitly mentioned in the job posting. This step resonates with setting protocol preferences in a network, where the primary language, like a primary protocol, ensures smooth operation.
3. Include Additional Languages
While not specified in this job description, including other languages you're fluent in can be a plus, especially in roles requiring communication with diverse teams. Think of these as auxiliary communication channels, adding layers of versatility to your profile.
4. Honest Proficiency Levels
Clearly differentiate your language proficiencies. Much like access levels in security settings, these distinctions (e.g., Native, Fluent, Intermediate, Basic) provide a clear understanding of your communication expertise.
5. Role's Scope and Languages
Consider the wider scope of the role. Even if not explicitly required, being multilingual in a cybersecurity role can sometimes be the difference between a good candidate and the perfect match, showcasing your ability to handle diverse challenges.
Takeaway
Your linguistic skills highlight your capability to navigate not only complex cybersecurity challenges but also the subtleties of cross-cultural communication. Showcasing this ability can significantly enhance your appeal as a candidate, opening doors to global opportunities.
Summary
Your CV's summary is like the decryption key to your professional narrative. It offers a sneak peek into your qualifications, experience, and what makes you the ideal candidate for the Security Analyst role. Let's ensure it's perfectly aligned with the job requirements.
1. Absorb the Job Essence
Immerse yourself in the job posting, understanding its core requirements and how they align with your expertise. This insight acts as the master key, unlocking the right approach to your summary.
2. Start with a Strong Intro
Kick off your summary with a clear and engaging introduction that captures the essence of your professional identity. Mention your years of experience and your specialization in IT security, setting the stage for a detailed showcase of your skills and achievements.
3. Address Key Requirements
Highlight your most relevant skills and accomplishments, drawing direct parallels to the job description. If the role emphasizes "network protocols" and "analytical skills," ensure these are prominently showcased in your summary.
4. Conciseness is Key
Keep your summary crisp and to the point. Aim for a concise yet powerful narrative that encapsulates your professional stature in a few impactful sentences. Remember, it's the teaser, not the full story.
Takeaway
Think of your summary as the gateway to your professional world. It's where you invite the hiring manager to explore further, providing just enough intrigue to delve into the details of your CV. Tailor it with precision, align it with the job requirements, and you'll have set the stage for a compelling application.
Launch Your Security Analyst Odyssey
You've now been armed with the tools and insights to craft a CV that doesn't just pass through ATS filters but captures the essence of what it means to be a Security Analyst. With Wozber's free CV builder, ATS-friendly CV templates, and ATS CV scanner, you're equipped to create an application that stands out and resonates with hiring managers. Your journey towards making the digital world a safer place is just beginning.
Let your CV be the beacon that guides you to your next great adventure. The cyber realm awaits your expertise.

- Bachelor's degree in Computer Science, Information Technology, or a related field.
- Minimum of 3 years of experience in IT security or related field.
- Proficiency with security tools such as SIEM, IDS/IPS, and vulnerability scanning solutions.
- In-depth knowledge of network protocols, network security tools, and anti-virus technologies.
- Strong analytical and problem-solving skills with the ability to communicate findings to both technical and non-technical stakeholders.
- Certifications such as CISSP, CISM, and Security+ are a plus.
- Must demonstrate strong English language competence.
- Must be located in New York, New York.
- Monitor security access and perform regular security assessments.
- Investigate any security breaches and carry out root cause analysis.
- Stay up to date with the latest security tools and vulnerabilities, and recommend security enhancements or purchases.
- Collaborate with IT and business teams to ensure security protocols and technologies are implemented effectively.
- Review and enforce security policies and procedures to safeguard company's data and systems.